AI In Cybersecurity Everything You Want To Know will be described in this article. Is AI able to assist cybersecurity defense against changing threats? Indeed. There has never been a more pressing need to protect networks, systems, and data from a variety of threats, including ransomware, phishing, and malware.
There’s hope thanks to artificial intelligence (AI). Artificial Intelligence (AI) is a fast evolving field that uses computers’ ability to learn, reason, and mimic human intelligence to make judgments.
AI In Cybersecurity Everything You Want To Know
In this article, you can know about AI In Cybersecurity Everything here are the details below;
Together, let’s explore how artificial intelligence (AI) is transforming threat identification and response by delving into the realm of cybersecurity. We’ll discover the exciting future possibilities of AI in protecting our digital world as we negotiate its possible biases, hazards, and ethical issues.
Understanding AI in cybersecurity
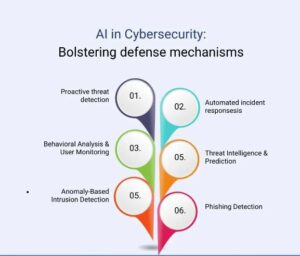
AI in cybersecurity:Bolstering defense mechanisms against cyber threats
1.Proactive threat detection:
AI is capable of real-time analysis of large books of data, identifying irregularities and possible dangers with a high degree of precision. This is due to AI’s ability to recognize patterns in data that humans are unable to, as well as its capacity to spot risks that conventional security technologies could overlook. AI can be utilized, for instance, to examine network data and spot unusual trends, such a lot of connections coming from a single IP address.
-
Automated incident response:
AI can handle incidents automatically, reducing damage and facilitating a speedy recovery. This is due to AI’s ability to recognize dangers and take appropriate action without requiring human involvement. AI can be employed, for instance, to automatically quarantine infected devices or to undo changes that a bad actor made.
-
behavioral analysis and User monitoring:
AI can identify questionable user behavior, defending against insider attacks. This is due to AI’s ability to recognize and understand deviations from typical user behavior. AI can be used, for instance, to determine whether a user is attempting to access private information from an unapproved location.
-
Threat intelligence and prediction:
AI can anticipate and stop possible threats by processing data related to threat intelligence. This is due to AI’s ability to learn about existing risks and apply that knowledge to recognize potentially unknown threats. AI, for instance, can be used to forecast which systems a specific threat actor is most likely to target.
-
Anomaly-based intrusion detection:
AI can identify zero-day attacks by spotting departures from typical behavior. This is due to AI’s ability to learn typical behavior and recognize abnormalities in it. AI, for instance, can be utilized to identify unusual system behavior, which may indicate a zero-day attack.
6. Improved phishing detection:
Artificial intelligence (AI) can examine emails and URLs to differentiate phishing attempts from authentic correspondence. This is so that it can recognize phishing attempts as AI is able to understand the traits of phishing emails and URLs. AI can be used, for instance, to determine whether an email is coming from a sender you should be wary of or whether a URL leads to a website that is harmful.
AI in Cybersecurity
Cybersecurity for threat detection, analysis, and respond
AI is utilized in cybersecurity for many reasons, such as:
- Threat detection: Compared to conventional techniques, AI can identify cyber threats more rapidly and precisely. This is accomplished by employing machine learning to study vast volumes of data and spot trends that might point to an impending attack.
- Threat analysis: Artificial intelligence (AI) can be used to examine and evaluate cyberthreats. Effective mitigation methods can then be developed using this information.
- Threat response: Artificial intelligence (AI) has the possibility to improve the speed and efficacy of cyber threat response. This is accomplished by automating the incident response process and identifying and blocking malicious traffic using machine learning.
- Network traffic analysis: Artificial intelligence (AI) finds harmful activity concealed in regular network traffic.
Examples of AI-powered cybersecurity tools and applications
Numerous AI-enabled cybersecurity solutions and programs are accessible, such as:
- CrowdStrike Falcon: Threat detection, analysis, and response capabilities are offered by this AI-driven cybersecurity platform.
- Palo Alto Networks Cortex XDR: This cybersecurity platform, driven by artificial intelligence, gives you complete visibility and control over your whole IT setup.
- QRadar for IBM Security with Watson: An AI-powered cybersecurity platform that offers threat intelligence, analytics, and automation is IBM Security QRadar with Watson.
AI-Driven Threat Detection
While there have been some successes with traditional threat detection techniques, there are a number of obstacles and restrictions with them. The vast amount of data produced by contemporary networks and systems is a major obstacle, making it challenging for human analysts to manually detect any risks in real-time.
Furthermore, rule-based detection systems are quickly circumvented by increasingly sophisticated cyber attacks. Organizations may become vulnerable to sophisticated threats if traditional procedures are unable to keep up with the quickly changing attack techniques.
False positives and false negatives can also impair threat detection accuracy, wasting time and money on non-threatening incident investigations or ignoring real threats.
Threat detection: Advanced pattern recognition and anomaly detection
AI-driven threat detection systems get around the drawbacks of conventional techniques by utilizing machine learning algorithms. Large volumes of data may be analyzed in real time by these systems, which can also identify trends and anomalies that could indicate possible security breaches.
AI algorithms are very good at spotting previously undiscovered attack vectors because they can learn from past data and adjust to new threats. AI-powered systems can identify zero-day attacks and other sophisticated threats that conventional methods might overlook because of their capacity to recognize odd patterns and behaviors even in the absence of clear rules.
Real-World examples: AI detecting cyber threats
- Network Intrusion Detection: Artificial intelligence (AI)-driven intrusion detection systems are able to keep an eye on network traffic, spot questionable activity, and find incursions through a variety of attack routes, including malware, phishing scams, and brute-force attacks.
- Behavioral Analysis: AI systems are able to examine user behavior and spot anomalies from the norm, which makes it possible to find compromised accounts or insider threats.
- Advanced Malware identification: AI is able to identify patterns and behaviors in malware that were previously undiscovered, which makes early identification and containment easier.
AI-powered security analytics
AI in processing and analyzing vast amounts of security data
Through the processing and analysis of massive amounts of data produced from various sources, including logs, network traffic, user activity, and endpoint events, artificial intelligence (AI) plays a critical role in security analytics. These data may be swiftly sorted through by the algorithms to find trends, anomalies, and possible security incidents. The workload for human analysts is greatly reduced by this automated analysis, which also makes it possible to react to new threats more quickly.
How AI-driven analytics helps in identyfing potential vulnerabilities
AI-driven analytics, by continuously monitoring and evaluating the IT environment, can find possible weaknesses and weak areas in an organization’s security posture. The algorithms are able to identify software that is out of date, configuration mistakes, and misconfigurations that could lead to security flaws.
AI analytics can prioritize significant vulnerabilities and give a comprehensive picture of the security landscape by combining data from many sources. This enables security teams to proactively remediate vulnerabilities.
Case Studies of AI-Based Security Analytics
- Automation of Incident Response: By identifying threats, evaluating their seriousness, and initiating the necessary actions, AI-powered security analytics can automate incident response. This speeds up response times, minimizes possible harm, and contains threats before they get out of hand.
- Threat Hunting: By identifying questionable patterns and emphasizing possible threat indicators, AI algorithms can support security analysts in their threat hunting efforts, increasing the effectiveness and efficiency of the hunt.
- Predictive security: AI-driven security analytics can forecast possible security threats and vulnerabilities by examining past data. This enables enterprises to fortify their defenses in advance by taking preventive action.
AI in incident response and mitigation
The manual procedure of traditional incident response can be laborious and prone to mistakes. The following actions are usually involved:
- Detection: Determining the existence of an incidence.
- Containment: Isolating the impacted systems and halting additional harm is known as containment.
- Investigating: Identifying the incident’s primary cause.
- Remediation: Remediation is the process of addressing the weakness that made the occurrence possible.
- Recovery: Recovery is the process of getting the impacted systems back to normal.
Many of these stages are accelerated and automated by AI-driven incident response. This can assist companies in minimizing damage and reaction times.
How AI automates and accelerates incident detection, containment, and recovery
There are several ways AI can be applied to automate and expedite event detection. AI can be used, for example, to keep an eye out for harmful activity in network traffic. It can also be used to examine user behavior to look for indications of deception.
Artificial Intelligence can be employed to the automate the containment process when an event has been recognized. This may entail preventing malicious traffic and isolating the compromised systems.
AI is also capable of automating the healing process. This may entail putting mitigating measures in place to stop such catastrophes in the future as well as returning the impacted systems to their initial state. Also check Aichatbot Alternatives
Challenges and risks of AI in cybersecurity
While artificial intelligence (AI) has demonstrated significant potential in improving cybersecurity, there are dangers and issues associated with AI that must be taken into consideration. Organizations using AI in cybersecurity procedures need to be mindful of the following possible hazards as they become more common:
Potential biases and limitations of AI algorithms
Since AI algorithms may only be as good as the data they are trained on, biased data may cause the AI system to reinforce and magnify its own prejudices. For instance, an AI cybersecurity model may miss new threats from other sources if the past data used to train it is skewed towards particular risks or attackers. Crucial actions to reduce this risk include making sure that training data is inclusive and diverse and routinely checking AI systems for biases.
Furthermore, the inability of AI systems to comprehend context and intent might result in false positives or negatives. This restriction could lead to the incorrect classification of benign activity as malevolent or vice versa. When analyzing AI-generated outcomes, cybersecurity experts need to exercise caution and double-check their findings with human experience.
Risk of AI being exploited by cyber attacters
Cybercriminals can take advantage of AI technology as they develop. AI, for example, can be used by attackers to plan and carry out increasingly complex operations that get past conventional cybersecurity measures. Artificial intelligence-generated deepfakes and synthetic content can also be used to trick consumers and get past security protections.
Organizations should concentrate on creating adversarial AI capabilities to recognize and thwart AI-driven assaults in order to mitigate this risk. In order to keep ahead of any nefarious application, AI models must also be continuously updated and monitored.
Ethics considerations in using AI for cybersecurity
AI-driven cybersecurity presents moral questions, especially in light of user monitoring and privacy. Enormous data collection and analysis for threat detection may violate people’s right to privacy. Finding the ideal balance between privacy and security is essential to upholding moral standards.
Gaining the trust of users also depends on AI algorithms being transparent and understandable. Stakeholders and users alike must comprehend how AI makes judgments and the rationale behind specific actions. In order to guarantee appropriate AI use in cybersecurity procedures, ethical rules ought to be defined.
Quick Evaluation of Application and Service Security | Application Architecture and Design
Furture prospects: AI and cybersecurity
AI has enormous promise in the cybersecurity space and presents a number of future prospects.
Predictions for furture of AI in the cybersecurity domain
It is anticipated that AI will play an increasingly bigger role in cybersecurity in the future. Cyber threat detection and mitigation will be facilitated by the increasing sophistication of AI-driven threat detection and response systems. AI will also be crucial in automating regular security chores, freeing up cybersecurity experts to concentrate on more difficult problems. Also check Ways To Send Large Files via E-mail
Countering emerging threats like AI-driven attacts
AI will be essential in thwarting AI-driven assaults as they materialize. As threats change, AI-powered security solutions will adjust accordingly, making it harder for hackers to take advantage of AI flaws. Anticipatory actions, like AI-powered ethical hacking, can also assist in locating and fixing possible flaws in AI-based cybersecurity systems.
Continuous research and development in AI for cybersecurity
Because cybersecurity is a dynamic field, AI research and development must be ongoing. AI specialists and cybersecurity specialists need to work together to improve the resilience, accuracy, and robustness of AI models. Investing in state-of-the-art AI technologies and providing cybersecurity personnel with continuous training is essential to staying ahead of cyber threats.
In summary
AI has the power to transform cybersecurity and increase its efficacy. Organizations may safeguard their networks, systems, and data by employing AI to detect and address cyber threats more swiftly and efficiently.
AI will drive cybersecurity in the future. Businesses that hope to stay on top of the game must spend money on cybersecurity solutions powered by AI.